Spectre and Meltdown in Hardware: Intel Clarifies Whiskey Lake and Amber Lake
by Ian Cutress on August 30, 2018 7:00 AM EST- Posted in
- CPUs
- Intel
- Spectre
- Meltdown
- Whiskey Lake
- Amber Lake
With the launch of Intel’s latest 8th Generation Core mobile processors, the 15W Whiskey Lake U-series and the 5W Amber Lake Y-series, questions were left on the table as to the state of the Spectre and Meltdown mitigations. Intel had, previously in the year, promised that there would be hardware fixes for some of these issues in consumer hardware by the end of the year. Nothing was mentioned in our WHL/AML briefing, so we caught up with Intel to find out the situation.
There Are Some Hardware Mitigations in Whiskey Lake
The takeaway message from our discussions with Intel is that there are some hardware mitigations in the new Whiskey Lake processors. In fact, there are almost as many as the upcoming Cascade Lake enterprise parts. Intel told us that while the goal was to be transparent in general with how these mitigations were being fixed - we think Intel misread the level of interest in the specifics in advance of the Whiskey Lake launch, especially when the situation is not a simple yes/no.
For the mitigations, here is the current status:
| Spectre and Meltdown on Intel | |||||
| AnandTech | Cascade Lake |
Whiskey Lake |
Amber Lake |
||
| Spectre | Variant 1 | Bounds Check Bypass | OS/VMM | OS/VMM | OS/VMM |
| Spectre | Variant 2 | Branch Target Injection | Hardware + OS | Firmware + OS | Firmware + OS |
| Meltdown | Variant 3 | Rogue Data Cache Load | Hardware | Hardware | Firmware |
| Meltdown | Variant 3a | Rogue System Register Read | Firmware | Firmware | Firmware |
| Variant 4 | Speculative Store Bypass | Firmware + OS | Firmware + OS | Firmware + OS | |
| Variant 5 | L1 Terminal Fault | Hardware | Hardware | Firmware | |
What this means is that Whiskey Lake is a new spin of silicon compared to Kaby Lake Refresh, but is still built on that Kaby Lake microarchitecture. Intel confirmed to us that Whiskey Lake is indeed built on the 14++ process node technology, indicating a respin of silicon.
As a result, both CPU families have the all-important (and most performance degrading) Meltdown vulnerability fixed. What remains unfixed in Whiskey Lake and differentiates it from Cascade Lake CPUs is Spectre variant 2, the Branch Target Injection. This vulnerability has its own performance costs when mitigated in software, and it has taken longer to develop a hardware fix.
What About Amber Lake?
The situation with Amber Lake is a little different. Intel confirmed to us that Amber Lake is still Kaby Lake – including being built on the 14+ process node – making it identical to Kaby Lake Refresh as far as the CPU die is concerned. In essence, these parts are binned to go within the 5W TDP at base frequency. But as a result, Amber Lake shares the same situation as Kaby Lake Refresh: all side channel attacks and mitigations are done in firmware and operating system fixes. Nothing in Amber Lake is protected against in hardware.
Performance
The big performance marker is tackling Spectre Variant 2. When fixed in software, Intel expects a 3-10% drop in performance depending on the workload – when fixed in hardware, Intel says that performance drop is a lot less, but expects new platforms (like Cascade Lake) to offer better overall performance anyway. Neither Whiskey Lake nor Amber Lake have mitigations for v2, but Whiskey Lake is certainly well on its way with fixes to some of the more dangerous attacks, such as v3 and L1TF. Whiskey Lake is also offering new performance bins as the platform is also on 14++, which will help with performance and power.
Intel’s Disclosure in the Future
Speaking with Intel, it is clear (and they recognise) that they appreciate the level of interest in the scope of these fixes. We’re pushing hard to make sure that with all future launches, detailed tables about the process of fixes will occur. Progress on these issues, if anything, is a good thing.
Related Reading
- Intel Launches Whiskey Lake-U and Amber Lake-Y
- Intel Discuss Whiskey Lake-U, Amber Lake-Y, and ‘Cascade Lake-X’
- Intel at Hot Chips 2018: Showing the Ankle of Cascade Lake
- Intel Wraps Up Spectre Patching, Partially Cancels Plans For 1st Gen Core & Core 2 Processors
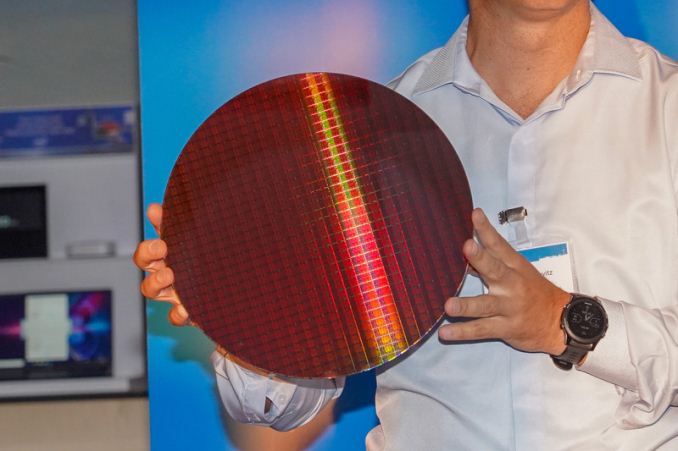
Title image from PC Watch










107 Comments
View All Comments
yeeeeman - Thursday, August 30, 2018 - link
I think you (the press) created the interest for these fixes, to have something to write/talk about. Other than real businesses, don't see anyone else to be really affected/interested by this.BurntMyBacon - Thursday, August 30, 2018 - link
In which case, I have to say kudos to Ian Et Al. for creating the interest that prompted Intel to be more forthcoming with this information.AdditionalPylons - Thursday, August 30, 2018 - link
Agreed.MrSpadge - Thursday, August 30, 2018 - link
+1Memo.Ray - Thursday, August 30, 2018 - link
It is OK, that guy still lives in 1983! Even HTTP hasn't been invented yet! no one is going to attack you :-)GekkePrutser - Sunday, September 9, 2018 - link
I as a consumer am very interested in this. I'm not really worried about the risk, but there was a drop in performance when the software patches were applied. I'm very interested in the hardware fixes' ability to reduce that drop.Ian Cutress - Thursday, August 30, 2018 - link
'Other than real businesses'Which would be 100% of businesses that exist? A large part of our audience? Or is that just the press creating interest? It's a funny move to strike out 100% of 'real' businesses and state we're the ones creating interest.
Icehawk - Thursday, August 30, 2018 - link
Can you convince my company that they need to address these exploits? Management has been ignoring the reports and basically refuses to patch anything.N Zaljov - Thursday, August 30, 2018 - link
I don't think that it's the job of a tech journalist to ensure that your company's head-honchos are responsible and foresightful people.The change of mind has to happen on a different level, and since the only way certain people learn is by burning their hands multiple times on a kitchen stove... ;-)
imaheadcase - Thursday, August 30, 2018 - link
That doesn't matter to normal people with technology. I know many people who just get something else if they can't figure out a problem within a few minutes.